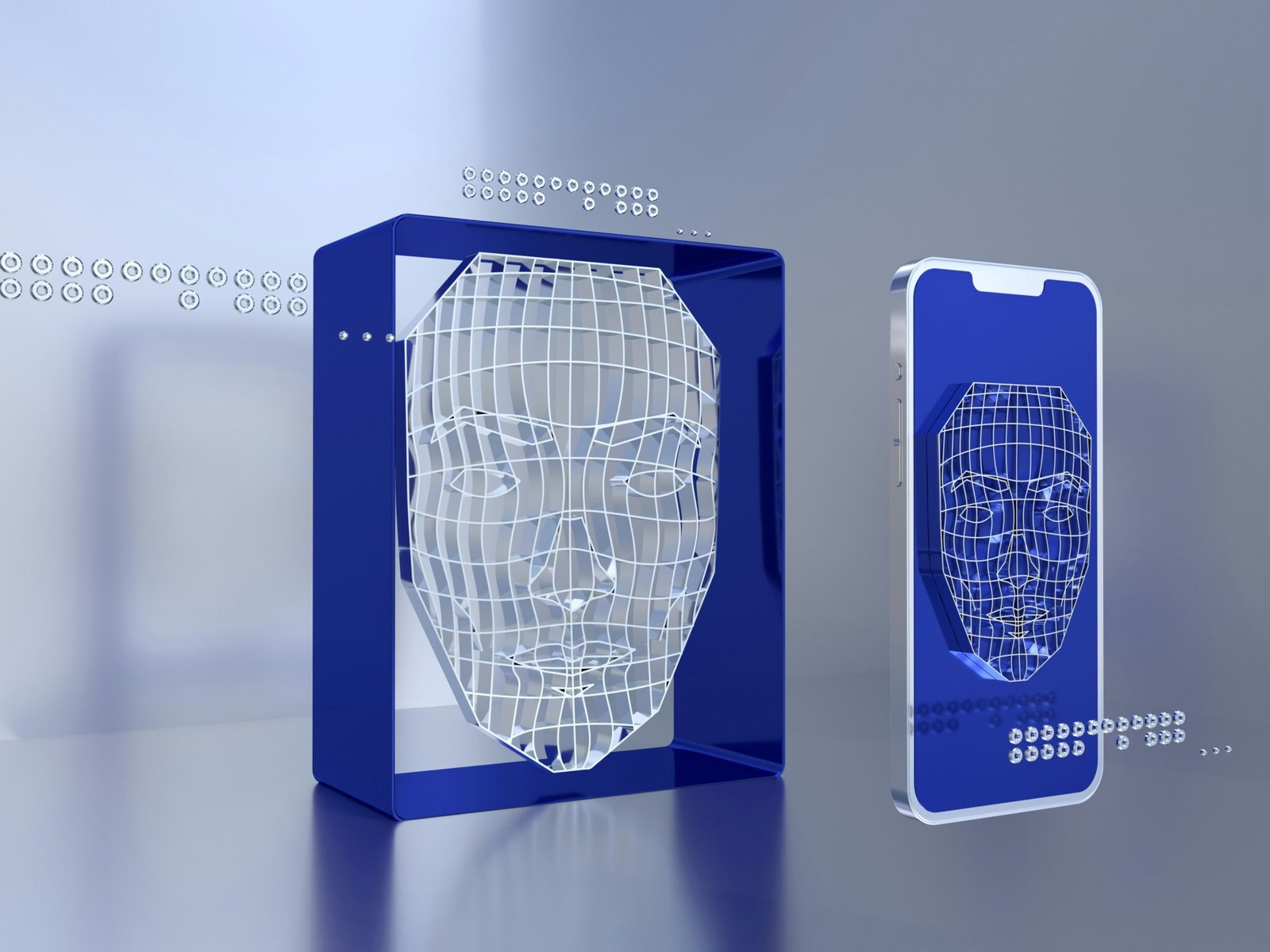
Behavioural biometric authentication involves identifying individuals through unique patterns in their interactions with devices, such as keystroke dynamics, mouse movements, touchscreen swipes, gait, and voice recognition. Unlike physical biometrics that rely on static traits like fingerprints or facial features, behavioural biometrics analyse continuous real-time activity, making it more adaptable to ongoing use.
A Data Privacy
Marcus White, Cybersecurity Specialist at Specops Software, explained, “Behavioural biometrics adds an innovative twist to traditional authentication methods by examining unique patterns in human activity. Unlike physical biometrics, which rely on static traits like fingerprints or facial structures, behavioural biometrics continuously verifies identity by analysing how you interact with devices in real time. Its continuous and unobtrusive nature makes it a perfect complement to existing security measures, filling in the gaps where traditional methods might fall short.”
Advanced solutions in this field now integrate artificial intelligence and machine learning, enabling systems to adapt to changes in user behaviour over time. By aggregating data on behaviours such as typing rhythm and mouse paths, these solutions create dynamic security profiles. AI-driven analytics can also combine behavioural data with contextual information like geolocation and device fingerprinting, offering real-time risk assessment.
Delving Into the Significance of Insider Transactions
The advantages of behavioural biometrics over traditional methods include continuous authentication, reduced risk of session hijacking, and the ability to detect fraud in real time. White stated, “Behavioural biometrics offer several advantages over traditional biometric methods by providing continuous, dynamic authentication with minimal disruption to the user. Instead of requiring a singular scan or snapshot of a physical trait, behavioural systems continuously monitor patterns such as keystrokes, mouse movements, or touchscreen interactions. This not only adds an extra layer of security by making it more difficult for attackers to spoof the system, but it also helps identify subtle anomalies or changes in behaviour that might signal a security breach.”
The passive nature of behavioural biometrics enhances user experience by reducing the need for frequent authentication prompts. These systems are capable of adapting to natural changes in behaviour, which may lower the chance of false rejections and streamline security processes for end users.